Microhills Inc.
Accelerating Your Digital Transformation
Best Solutions for
Web Designs, Apps, Business Transformation, Workforce, and Technology Consulting
We can solve your business challenges with Software Solutions, Business Transformation, Workforce, and Technology Consulting
Microhills Inc is the partner of choice for many of the world’s leading
enterprises, SMEs and technology challengers. We help businesses elevate their value through
custom software development, web design, Cybersecurity, Artificial Intelligence Solutions, Data Management, Business Transformation, Workforce, and Technology consulting.
SERVICES
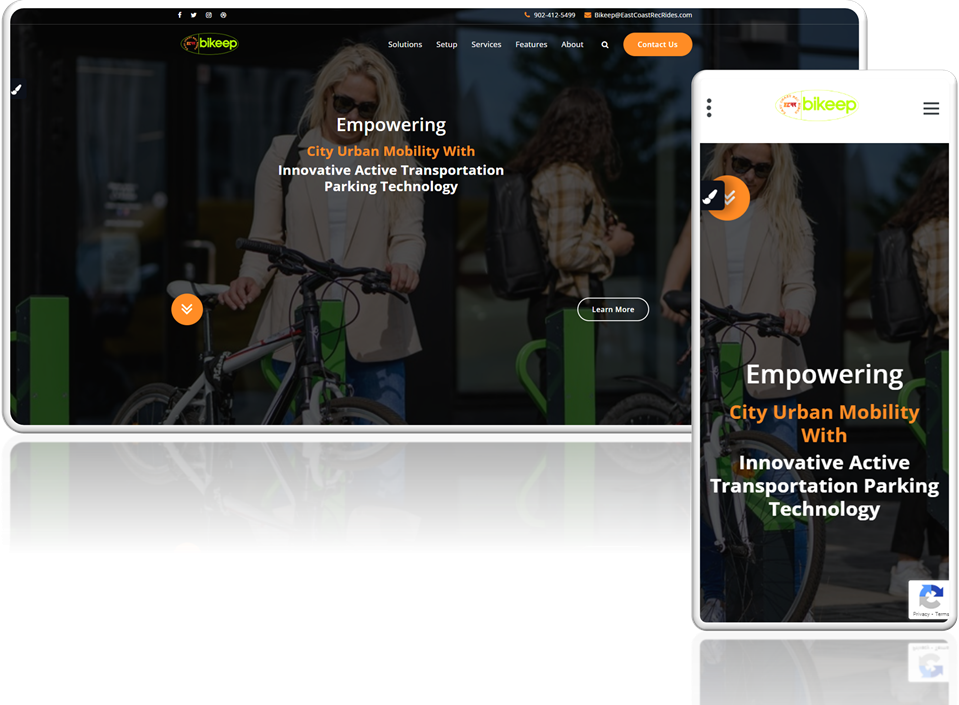
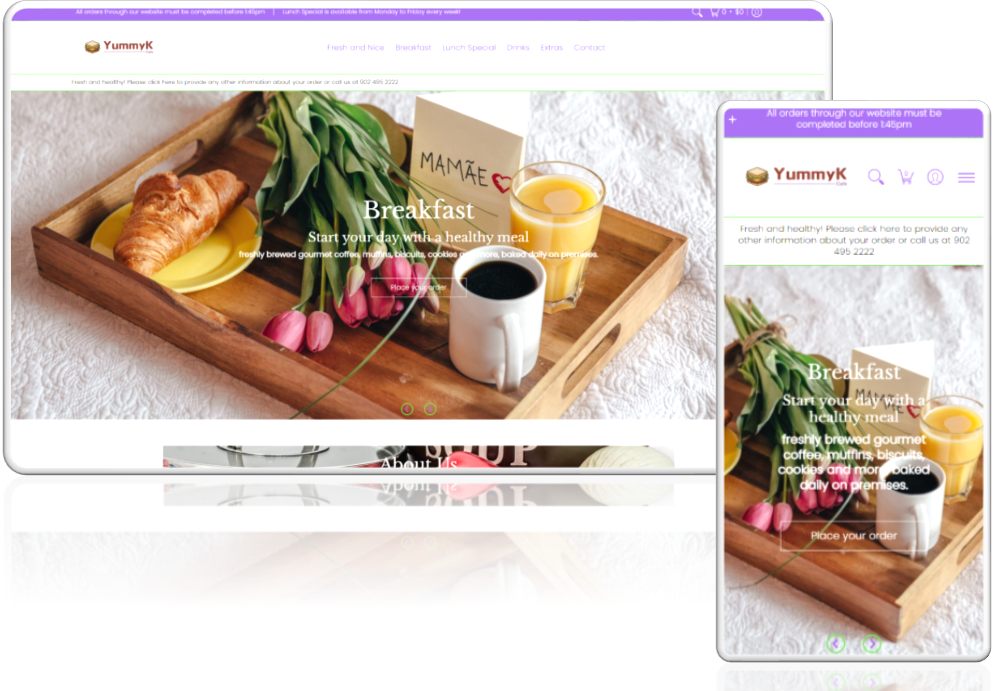
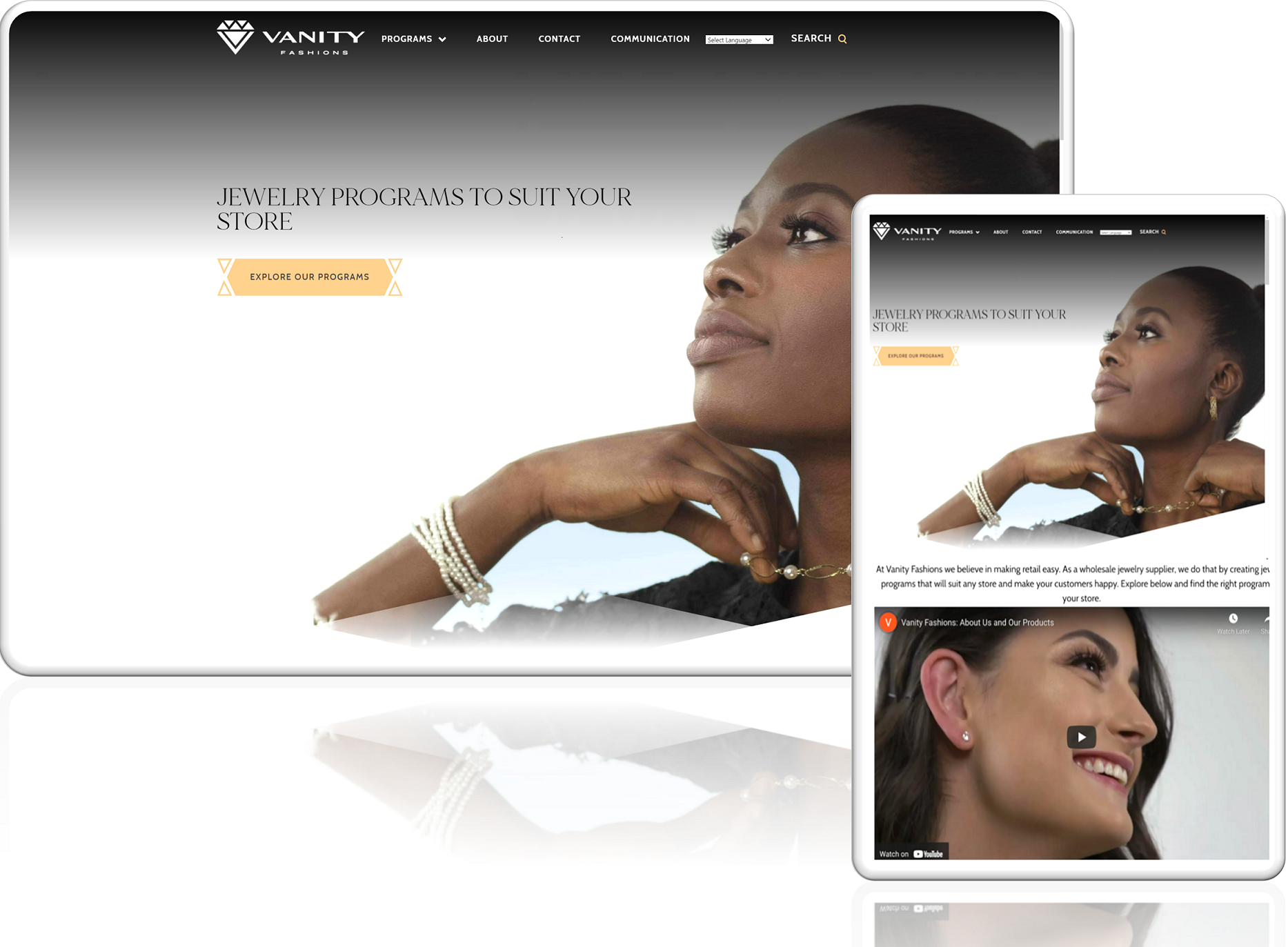
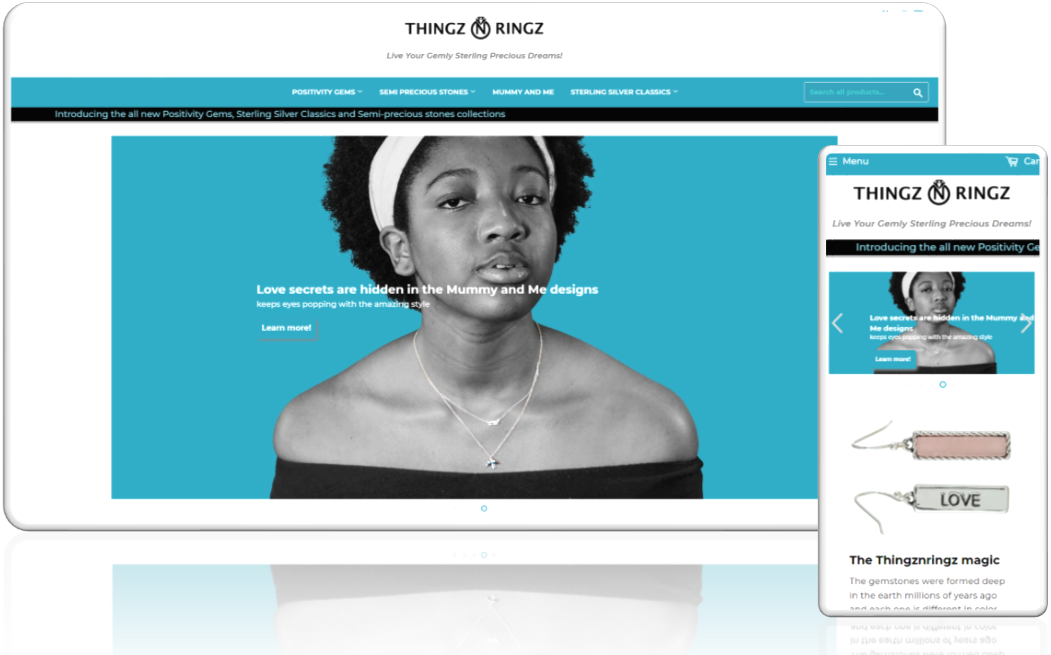
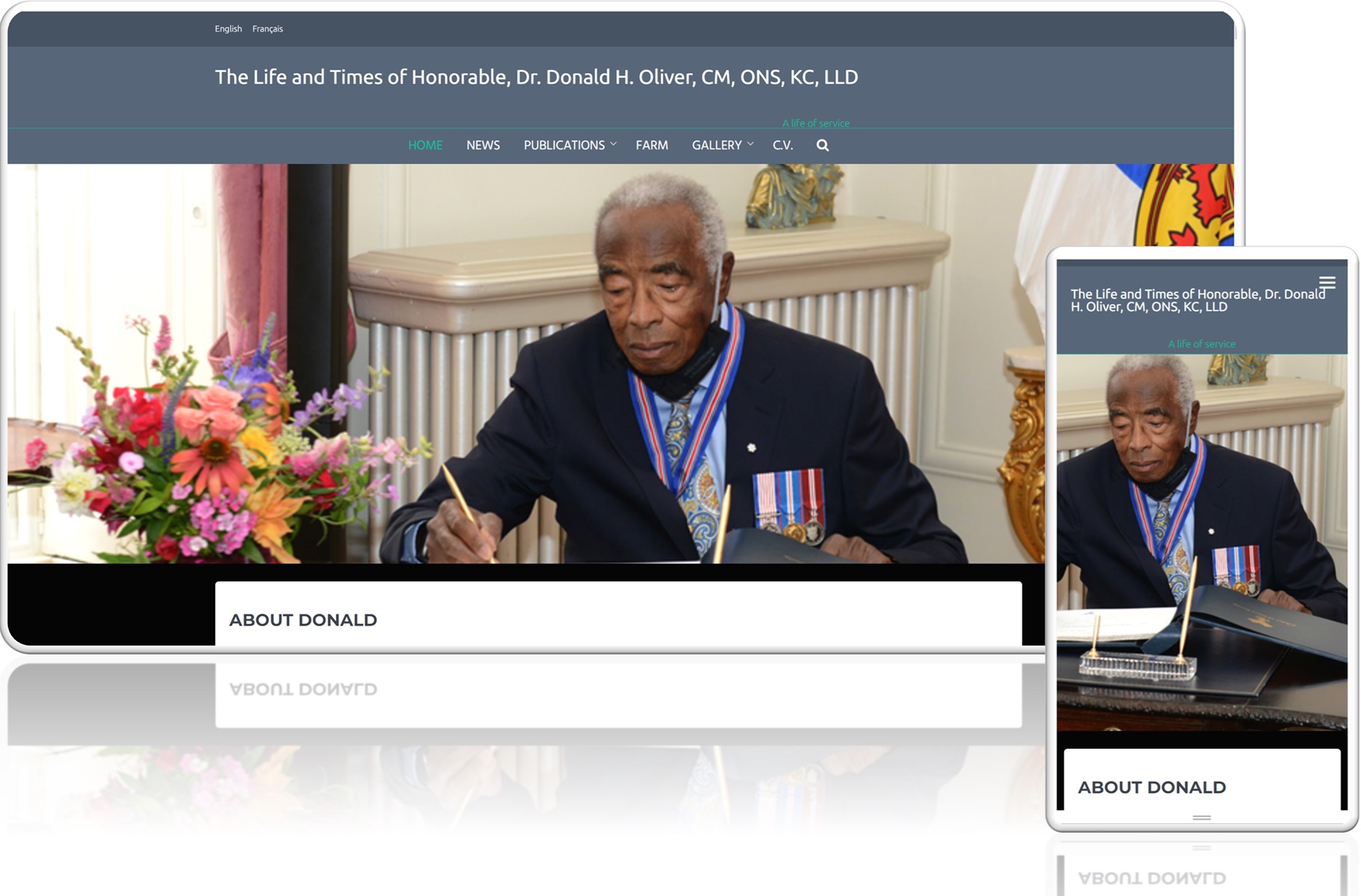
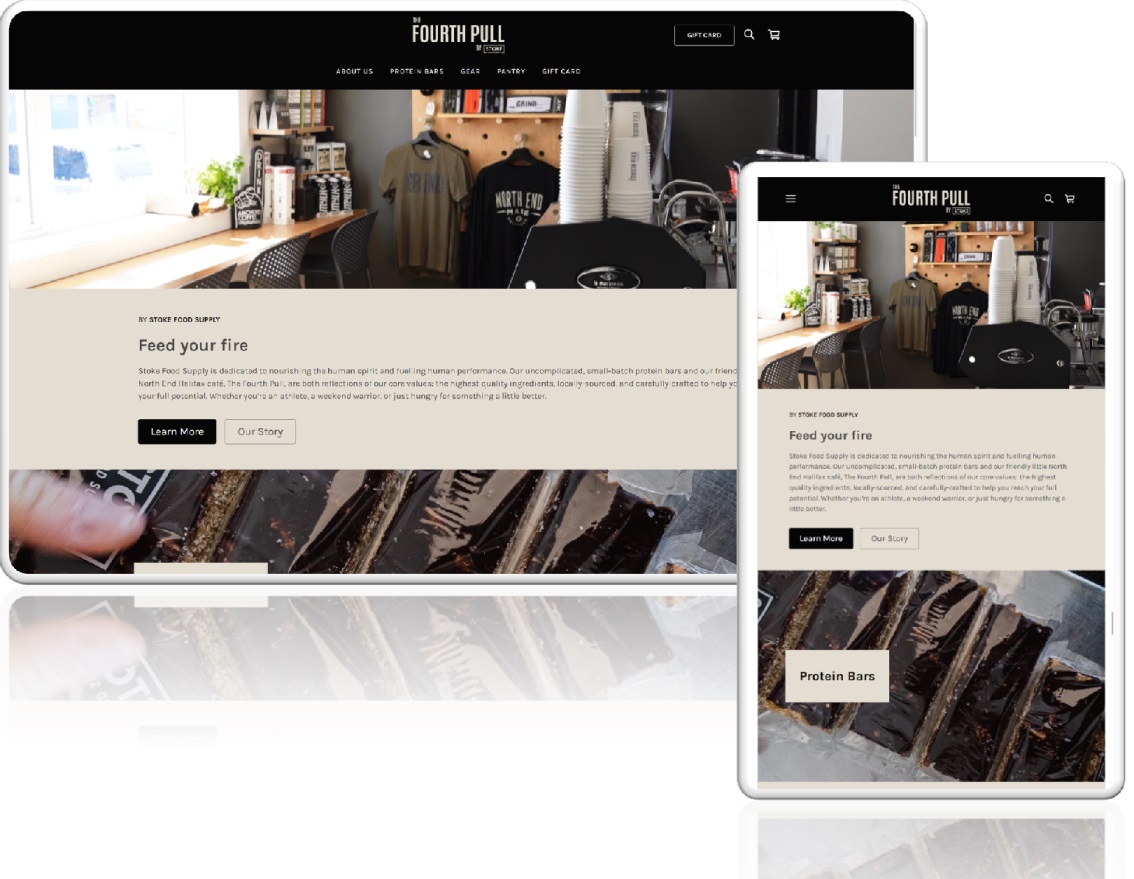
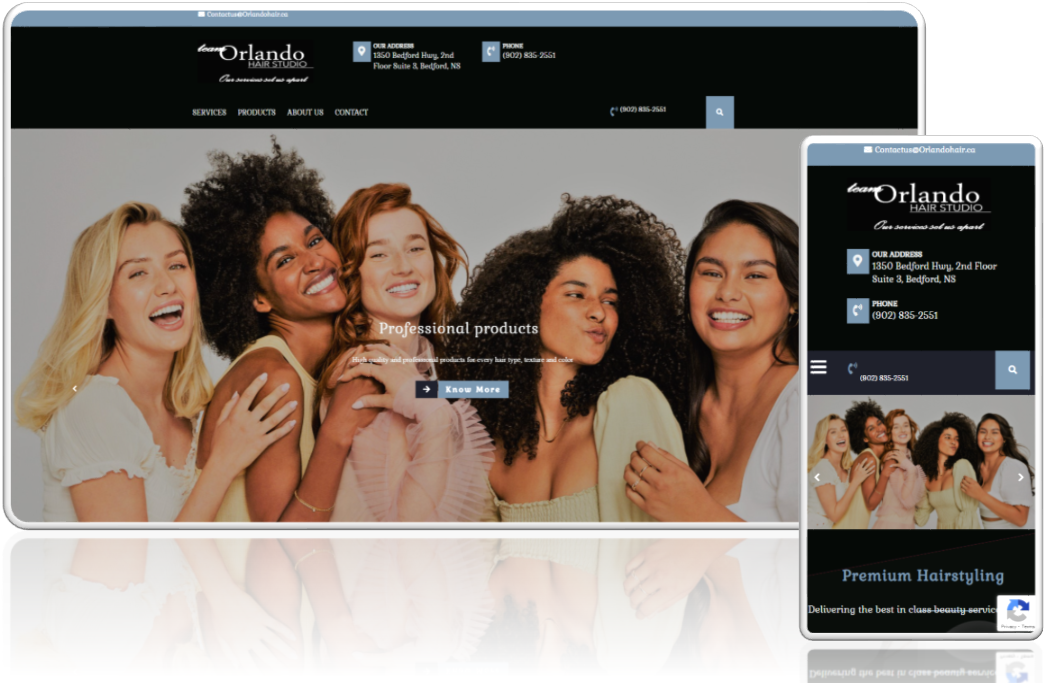
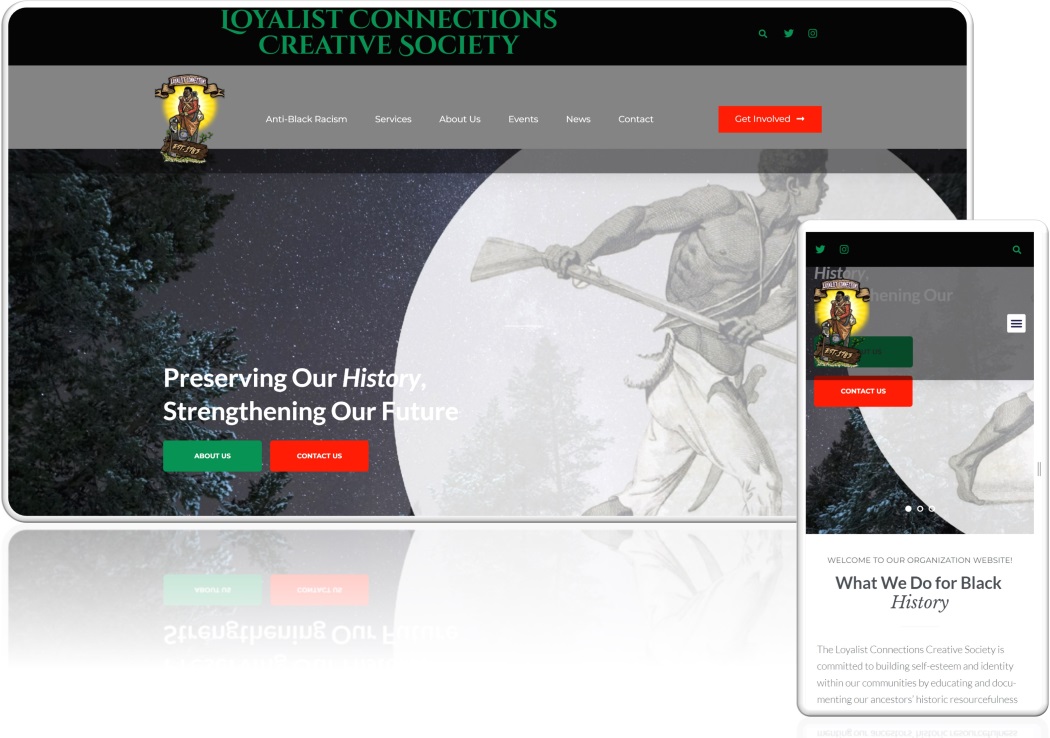
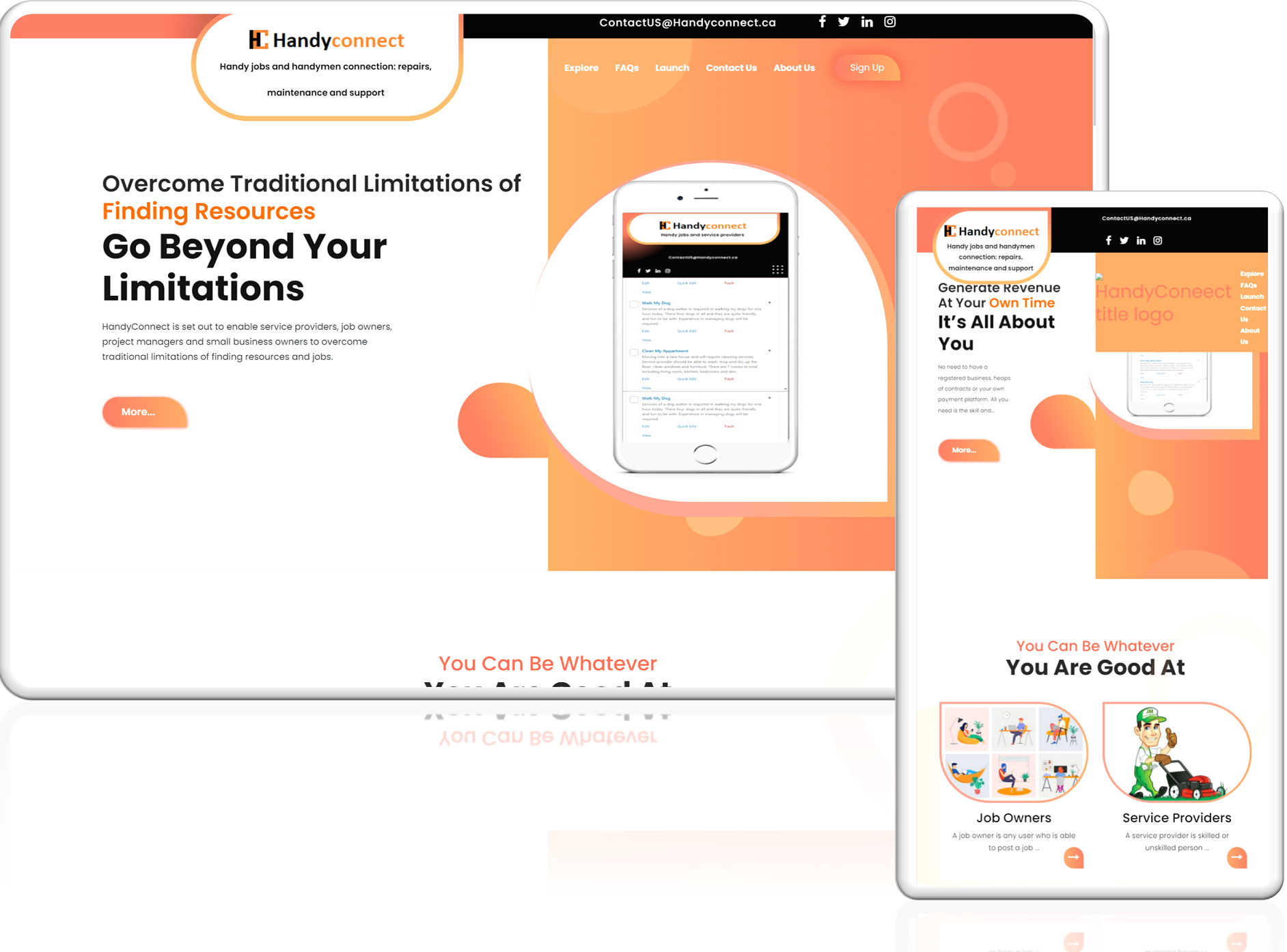
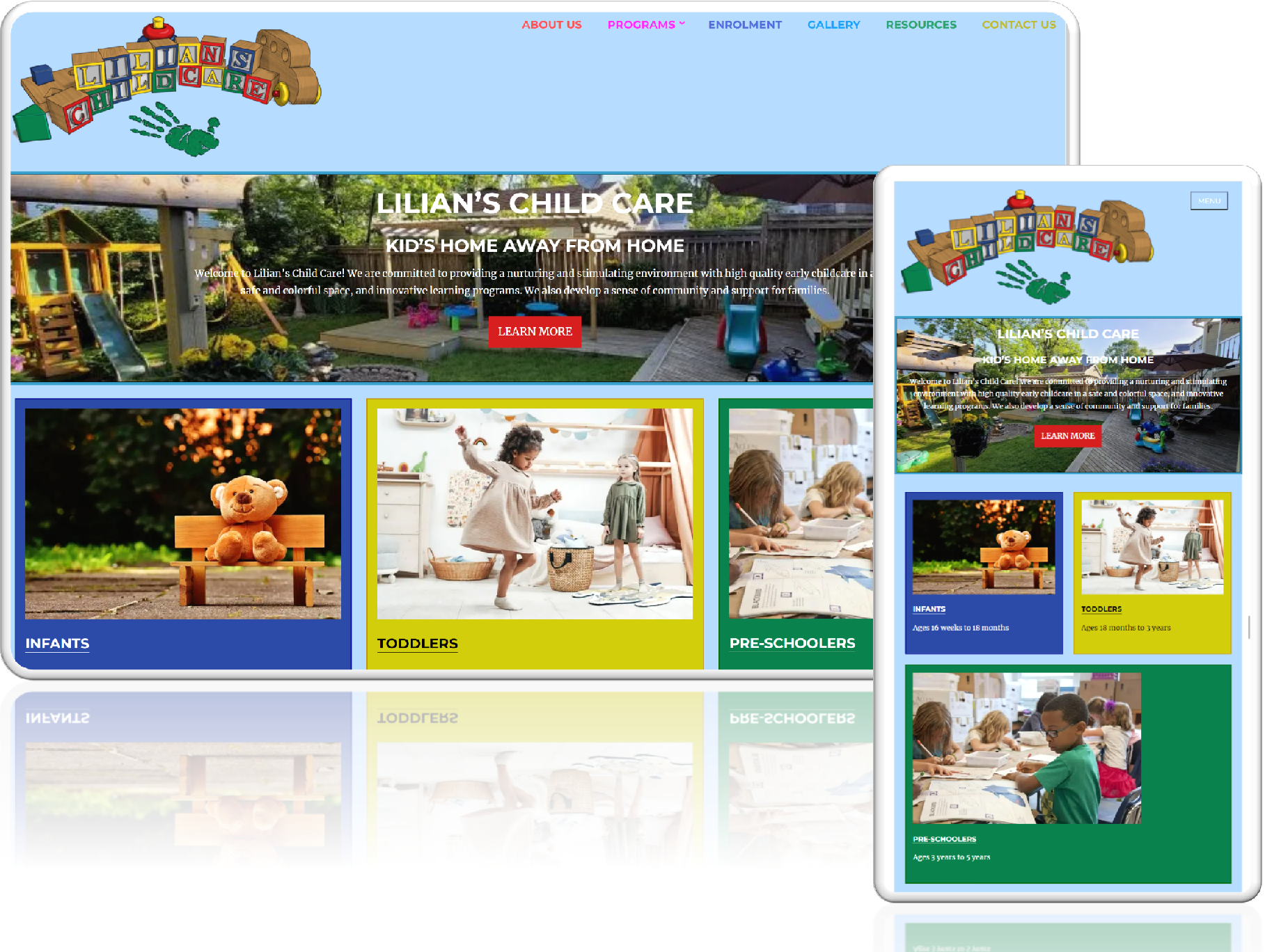
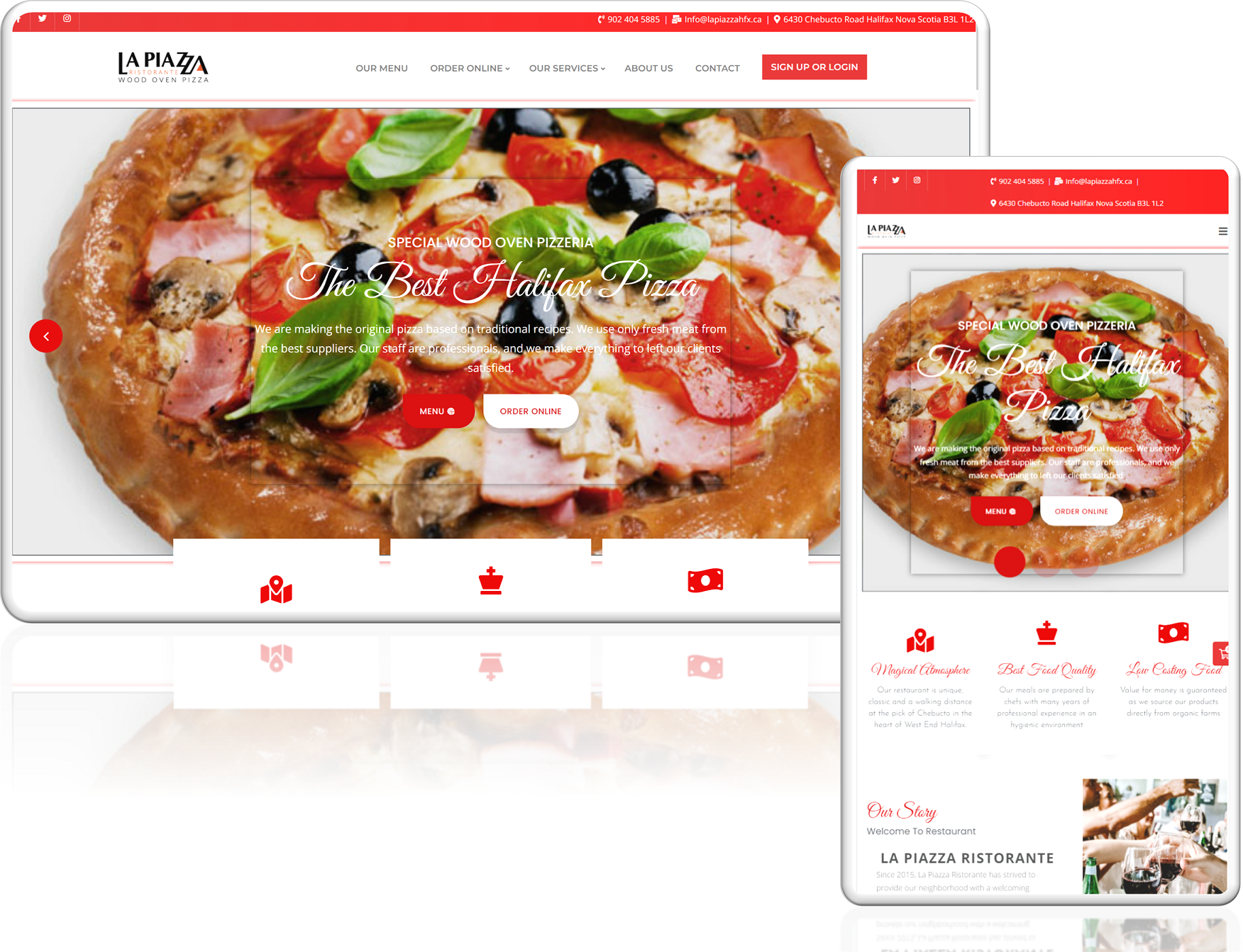
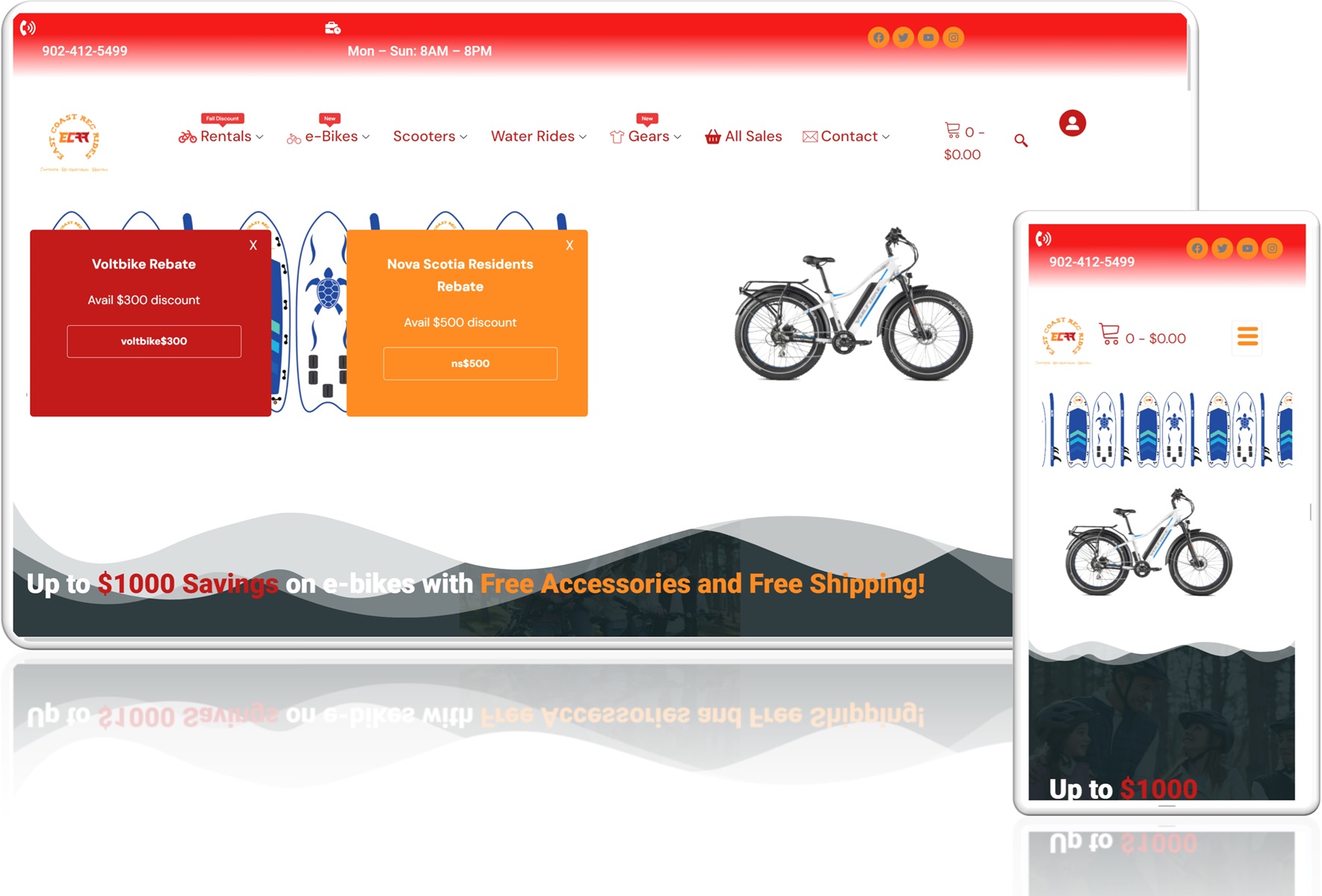
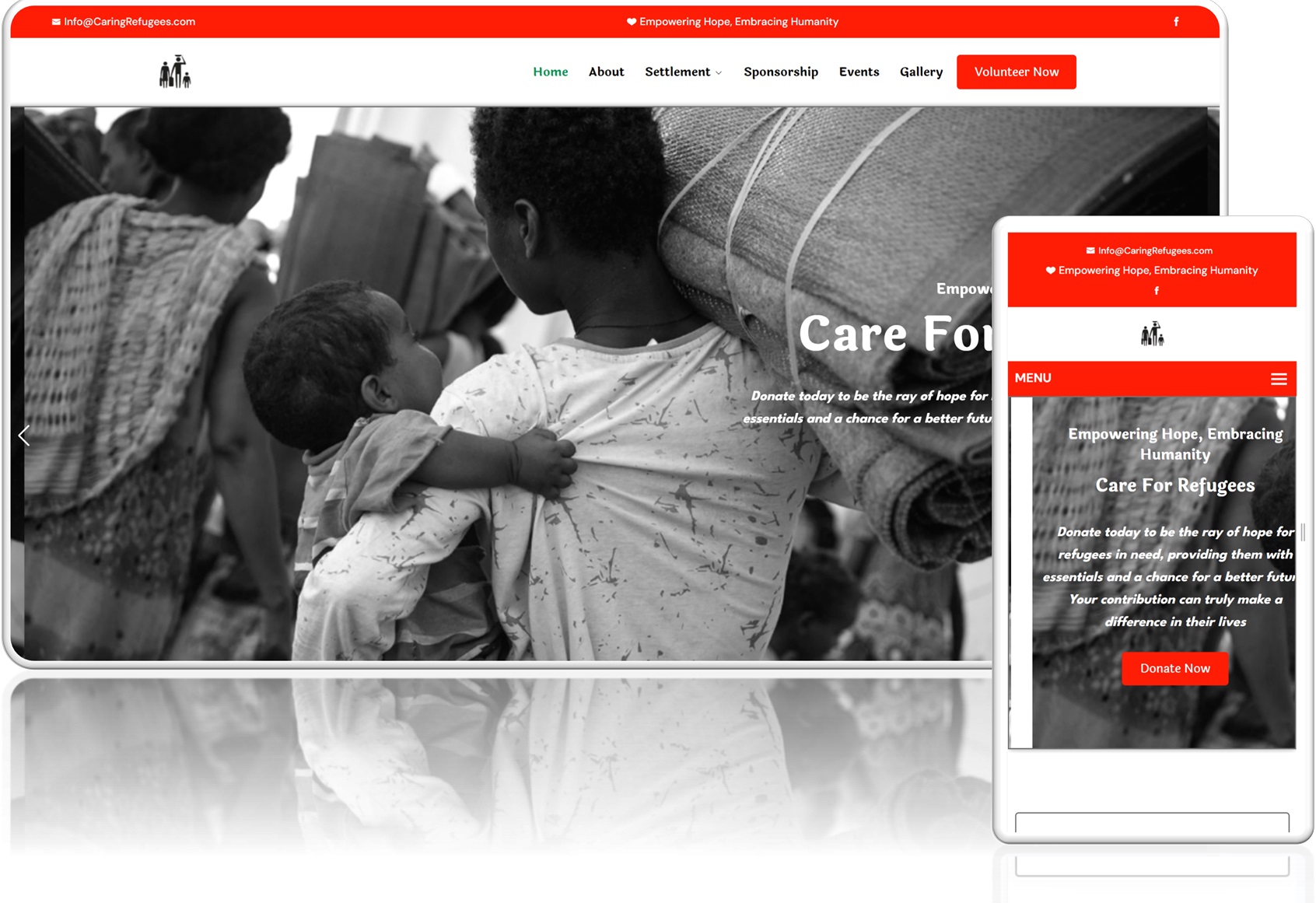
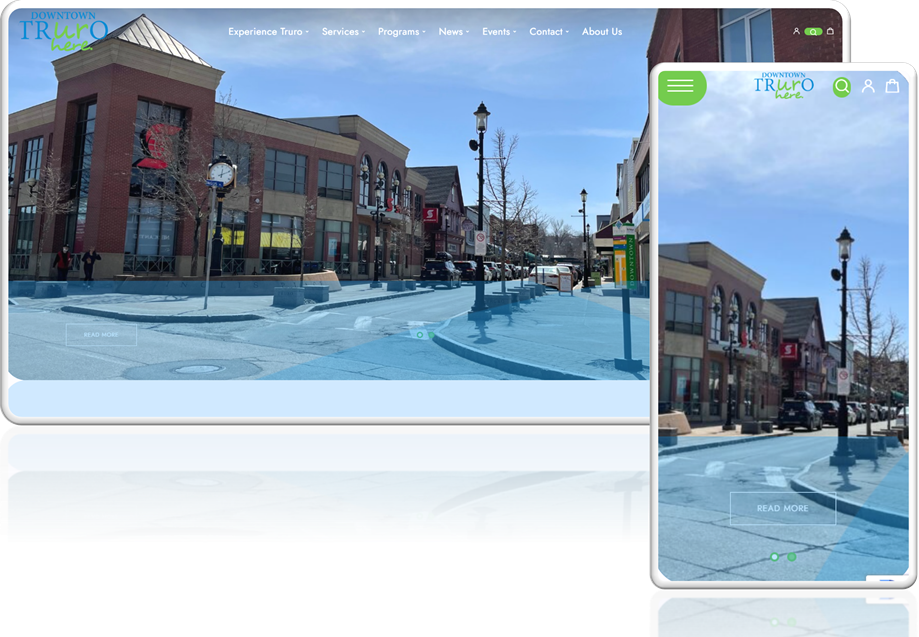
Website Design
We provide best web designs with lifetime maintenance and support of business as stragegy, management, etc

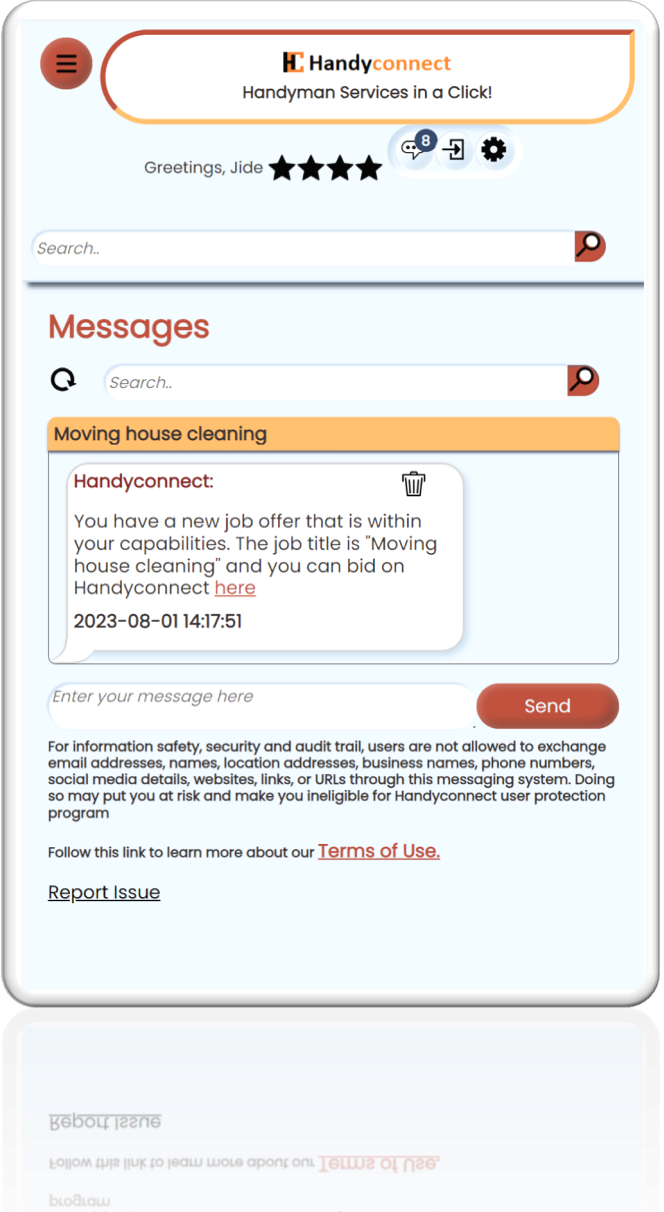
Software Development
Our software development team ensure a fit-for-purpose design that meets business requirements.

Cybersecurity Solutions
We specialize in comprehensive cybersecurity solutions designed to protect your business from the inside out. Our services are tailored to address your unique vulnerabilities, minimize risks, and ensure your organization stays one step ahead of cybercriminals.

Biometrics Services
We assure you of fast and secure biometrics data collection and transmission with state of the art equipment and amazing customer experience

Photography and Videography
Our professional photographers will ensure high quality images and videos for your website development and marketing

Technology Consulting
We provide expert guidance, solutions, and recommendations to organizations seeking to optimize their technology infrastructure, streamline processes, and achieve their goals using the right tools. These services bridge the gap between business needs and technological implementation, ensuring clients make informed decisions about their technology investments.

Business Transformation
The radical changes in client satisfaction requires innovation ways of doing things differently. We specialize in helping organizations achieve extraordinary results through digital transformation by designing and implementing workflows that improve business result.

Workforce Consulting
The radical changes reshaping the world of work are not limited to pandemic, disruptive technological innovation, business risks, and regulations but also skills mismatches, talent, and human resource challenges. We specialize in helping organizations achieve extraordinary results through enhancing workforce effectiveness, and developing critical talent.
Works
WHY CHOOSE US
WE CREATE DIFFERENTIATED VALUE TO INCREASE YOUR BUSINESS PERFORMANCE

EXPERT KNOWLEDGE
Over 45 years of combined IT industry experience.

PASSION FOR YOUR SUCCESS
We are passionate about helping you to achieve your business goals.

END-2-END
Best-in-class end-to-end information technology services.

UNLIMITED SUPPORT
Unlimited post-implementation support and training for all solutions.
45
Years of
Experience
Experience
1565
Projects
completed
completed
240
Satisfied clients on
24 countries
24 countries
REVIEWS
“Microhills’ Experts provided perfect IT solutions. Fast response and affordable pricing.
We’re really satisfied!”

Conor M.
Senior Marketing at Amazon
“ Amazing web designs from Microhills’ experts. They are the best!”

Elvis J.
Senior Marketing Manager at ECRR
PRICING & PLAN
 MAINTENANCE AND SUPPORT
MAINTENANCE AND SUPPORT
49.99 / yearly
550 / yearly
- DIGITAL MARKETING
- BACKUP & RECOVERY
- CYBERSECURITY
- EXPERT CONSULTANCY
Recommended  WEBSITE DESIGN
WEBSITE DESIGN
6500 / project
6500 / project
- E-COMMERCE
- PHOTOGRAPHY
- VIDEOGRAPHY
- PAYMENT SOLUTIONS
- LIFETIME SUPPORT
- SEO & MARKETING
 APPS DEVELOPMENT
APPS DEVELOPMENT
7999 / project
7999 / project
- MOBILE APPS
- WEB APPS
- WORKFLOWS
- INTEGRATIONS
- lifetime support
Do you have a large team? Contact us for information about more enterprise options












EDITORIAL
Payment System
Description: The With Microhills Payment App provides hundreds of payment gateways for your customers. From PayPal to Stripe to Sk...
Software Selection
Software Selection Webinar delivered to tourism businesses in Nova Scotia in partnership with Digital Nova Scotia. In this present...
Read MoreLet us partner with you to achieve your business goals!
(+1) 902 903 0050
contactus@microhills.com
Suite 100, 6156 Quinpool Road, Halifax, Nova Scotia. B3L 1A3